Networking & Cloud Computing
epub |eng | 2013-12-11 | Author:Todd Lammle
Here is the command syntax you use to add a static route to a routing table from global config: ip route [destination_network] [mask] [next-hop_address or exitinterface] [administrative_distance] [permanent] Router(config)#ip route ...
( Category:
Networks, Protocols & APIs
April 14,2014 )
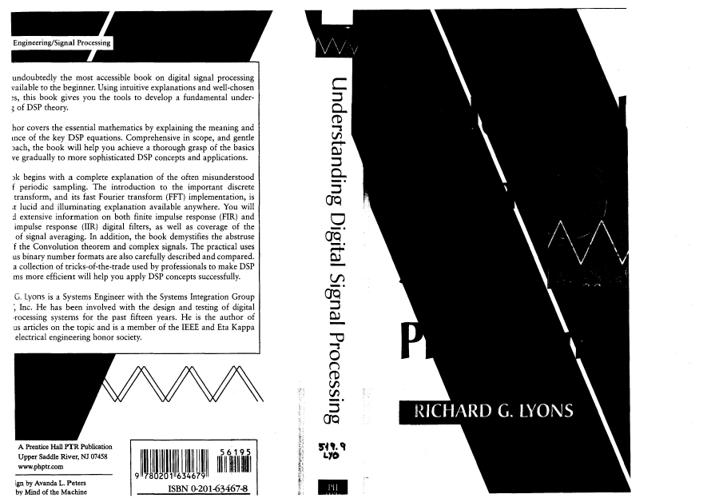
epub, pdf |eng | 2011-04-08 | Author:Richard G. Lyons
For computational efficiency reasons, to avoid unnecessary arithmetic using the imaginary parts of the complex C values, we might decide to compute Q as Show the validity (the correctness) of ...
( Category:
Signal Processing
April 9,2014 )
epub |eng | 2011-06-12 | Author:Nelson-Smith, Stephen [Stephen Nelson-Smith]
* * * [21] https://github.com/wycats/thor [22] For more complex requirements, or sometimes just because the test suits it, the “controller” container can be used for the verification portion of tests. ...
( Category:
Network Administration
April 6,2014 )
epub |eng | 2011-08-15 | Author:LeBlanc, Jonathan [Jonathan LeBlanc]
oauth_authorization_expires_in The lifetime of the oauth_session_handle in seconds oauth_expires_in The lifetime of the token in seconds Once we’ve created an access token object out of the provider’s response, our application ...
( Category:
Networking & Cloud Computing
April 6,2014 )
epub |eng | 2010-11-11 | Author:Hewitt, Eben [Eben Hewitt]
Thrift Summary If you want to use Thrift directly for your project, there are numerous prerequisites for working on Windows (see http://wiki.apache.org/thrift/ThriftInstallationWin32) and many things that can go wrong. Partly ...
( Category:
Data Mining
April 6,2014 )
epub |eng | 2011-08-24 | Author:Hartpence, Bruce [Bruce Hartpence]
The Rapid Spanning Tree Protocol The Spanning Tree Protocol from IEEE 802.1D is highly effective at eliminating loops but very slow at converging in other situations such as recovering pathways. ...
( Category:
Networks, Protocols & APIs
April 6,2014 )
epub |eng | 2010-03-04 | Author:Beijnum, Iljitsch van [Iljitsch van Beijnum]
Smurf directed broadcast amplification “Smurf” attacks use misconfigured intermediate networks to multiply traffic, allowing attackers to easily muster up large amounts of traffic without the need to hack any systems. ...
( Category:
Networks, Protocols & APIs
April 6,2014 )
epub |eng | 2011-06-02 | Author:Hartpence, Bruce [Bruce Hartpence]
Node A MAC 1 1 Node B MAC 1 2 Node C MAC 1 3 Node D MAC 1 4 A switch has some basic procedures to follow: When a ...
( Category:
Networks, Protocols & APIs
April 6,2014 )
epub |eng | 2011-01-27 | Author:Warden, Pete [Pete Warden]
Wolfram Alpha The Wolfram Alpha platform pulls together a very broad range of facts and figures on everything from chemistry to finance. The REST API takes in some search terms ...
( Category:
Storage & Retrieval
April 6,2014 )
epub, mobi |eng | 2009-12-14 | Author:Schmitt, Christopher [Christopher Schmitt]
( Category:
CSS Programming
April 6,2014 )
epub |eng | 2012-03-04 | Author:Schwartz, Baron, Tkachenko, Vadim, Zaitsev, Peter & Peter Zaitsev & Vadim Tkachenko [Baron Schwartz]
When Should You Use Flash? The most obvious use case for solid-state storage is any workload that has a lot of random I/O. Random I/O is usually caused by the ...
( Category:
Performance Optimization
April 6,2014 )
epub, mobi |eng | 2011-07-24 | Author:Pepple, Ken [Ken Pepple]
API Nova features a pluggable architecture for API support. The current Nova incarnation supports: OpenStack API 1.0 (with preliminary OpenStack 1.1 API support) Amazon EC2 API Many customers will probably ...
( Category:
Networking & Cloud Computing
April 6,2014 )
epub |eng | 2009-02-08 | Author:Company, Sonatype [Sonatype Company]
The includes section uses a list of include elements, which contain path patterns. These patterns may contain wildcards, such as **, which matches one or more directories, or *, which ...
( Category:
Software Development
April 6,2014 )
epub |eng | 2009-02-08 | Author:Chandra, Pravir, Messier, Matt, Viega, John & Matt Messier & Pravir Chandra [John Viega]
type The operation to perform, which can be one of the following constants: EVP_CTRL_GET_RC2_KEY_BITS EVP_CTRL_SET_RC2_KEY_BITS EVP_CTRL_GET_RC5_ROUNDS EVP_CTRL_SET_RC5_ROUNDS arg The numerical value to set, if appropriate. If not appropriate, its value ...
( Category:
Network Security
April 6,2014 )
epub |eng | 2010-11-01 | Author:Hansteen, Peter N.M. [Peter N.M. Hansteen]
Updating Lists If you run spamdb without any parameters, it lists the contents of your spamdb database, and it lets you add or delete both spamtrap addresses and traplist entries. ...
( Category:
Networking & Cloud Computing
April 6,2014 )
Categories
Popular ebooks
The Mikado Method by Ola Ellnestam Daniel Brolund(25056)Kotlin in Action by Dmitry Jemerov(22280)
Grails in Action by Glen Smith Peter Ledbrook(18426)
Sass and Compass in Action by Wynn Netherland Nathan Weizenbaum Chris Eppstein Brandon Mathis(15745)
Configuring Windows Server Hybrid Advanced Services Exam Ref AZ-801 by Chris Gill(7539)
Azure Containers Explained by Wesley Haakman & Richard Hooper(7524)
Running Windows Containers on AWS by Marcio Morales(7079)
Microsoft 365 Identity and Services Exam Guide MS-100 by Aaron Guilmette(5459)
Microsoft Cybersecurity Architect Exam Ref SC-100 by Dwayne Natwick(5304)
Ember.js in Action by Joachim Haagen Skeie(5227)
Combating Crime on the Dark Web by Nearchos Nearchou(5060)
The Ruby Workshop by Akshat Paul Peter Philips Dániel Szabó and Cheyne Wallace(4734)
Management Strategies for the Cloud Revolution: How Cloud Computing Is Transforming Business and Why You Can't Afford to Be Left Behind by Charles Babcock(4581)
The Age of Surveillance Capitalism by Shoshana Zuboff(4314)
Python for Security and Networking - Third Edition by José Manuel Ortega(4309)
Learn Windows PowerShell in a Month of Lunches by Don Jones(4305)
Learn Wireshark by Lisa Bock(4201)
The Ultimate Docker Container Book by Schenker Gabriel N.;(3949)
DevSecOps in Practice with VMware Tanzu by Parth Pandit & Robert Hardt(3642)
Windows Ransomware Detection and Protection by Marius Sandbu(3615)